Can a Microchip be copied and replicated without permission? How is this possible?
Here I will explain the Reasons and Techniques to avoid it!
With the today global market of integrated circuits and a longer IC supply-chain involving several partners, security vulnerabilities are appearing.
Techniques of reverse engineering can be utilized also in the tiny fabricated chips or more easily in exported layout gds-files.
There are much valious information for the competitors: design techniques, materials, performance, functionality, etc… or just because they want to copy it and use it implicitly.
More a more cases are coming out
This is not paranoia, the cases are increasing. In 2010 VisionTech was revealed to sell counterfeit chips for military use stolen in Hong Kong and China. It is said that they make more than 15M$. In 2019, the company Bloke that admits to copy and sell chips which are used in the B-1 American bomber.
In the White Paper from the Semiconductor Industry Association (section IV), they enumerate real known cases of health, safety, and security detected issues
Chip Reverse Engineering: Analog vs. Digital
In circuit design, we can distinguish between 2 very different parts and worlds: analog and digital.
With previous chip technologies, it was easier to retrieve the schematic and netlist from a chip. Circuits were simpler and bigger. In 1975 the standard transistor size was 6 μm (begins of the Moore’s Law), when now analog circuits are made in 180 nm or even lower with 130 nm, 90 nm or 65 nm (for digital circuits maybe 10 nm or 7 nm). The size is smaller but also the technologies are more complex with more layers.
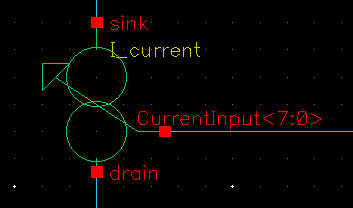
Analog parts are the most copied because the…
reduced count of transistors
lack of effective defense techniques
From the layout, it is very easy to extract patterns to generate a copied schematic view.
In digital blocks, on the other hand, the number of transistors increases considerably up to millions. Also, the locking techniques are well developed, it is almost improbable to counterfeit a digital part.
Many protect techniques
Millions of transistors
where is the layout coming form?
3 options:
For some malicious foundries, it is simple to obtain an analog block coming from an exported layout file (gds-II layout format file).
Some hackers could access to the servers where the circuits are stored or they can be leaked internally from the company coworkers.
The direct way: despackage and scan the chip layer by layer:
-Wooow. Yes?
-Yes
-How?
The process involves the decapsulation or unpack of the fabricated chip. Later apply a delayering method that consists in stripping off the chip regarding its metal layers.
For each metal layer many pictures are taken to later create a huge layer picture for post-processing. The imaging process is performed identifying the components like transistors, resistors, logic gates, memory cells, capacitors, etc. Next step is the interconnections of the components to obtain finally the schematic.
Why we would like to protect our IP?
An IP (Intellectual Property) is a block or a part of a circuit in charge of doing some specific task: An ADC converter, LDO, a comparator, a microcontroller core, a memory cell, etc.
The IC supply chain extension
Traditionally, chip makers design and fabricate their own chips, remaining all the IC-supply in-house. But nowadays the physical production of the microchip is carried out by third-part companies, and more and more chip companies are going fabless. This is extending the IC-supply chain to many different vendors and involving companies from the other part of the world. The fabrication also is outsourced in all the research centres or universities.
Usually, we can find 3 stages in the supply IC-chain: IP vendors, IC fabless designers and foundries.
What are the IP copies used for?
Implicit illegally use of the IP: Directly use the IP without the knowledge and consent of the designer.
IC overproduction: You are a fabless company and send your chip (for example a novel RFID tag) to fabricate 20,000 copies. The foundry manufacture 30,000 chips, send to you your 20,000 chips and sell in the gray market the rest of microchips.
Avoid overproduction of IP. Companies buy the right to produce 1 million devices of a block (let’s say an ADC converter).
Later after a time, the same company want to integer the same ADC block in other design, but they do not have the right to use any more. Also if they want to reproduce the previous design without authorization.
Mask sell: Malicious fabs can reuse the mask or sell this original design to a third party to make a profit.
Release of defective parts: After a chip is fabricated, a test is performed, and the chip that no fulfill the specs, they are dismissed. Again some untrusted foundries could sell this defective chips, that does not work 100% as expected, but still give some performance.
Competitors espionage: You can reverse-engineer other IPs and try to mimic it or even improve it to create your product.
Hardware Trojans: The knowledge of the circuit can give the possibility to make malicious modifications to alter the functionality of the chip. This is relevant for special military or safety-critical civilian applications.
Hardware Trojans are very hard to find. Last big case was when China was inserting small chips in the US servers to infiltrate and open a back door.
For example, with the so-called dopant-trojans, any optical analysis will detect the modification. Adding or removing some dopant regions to the circuit will change its behaviour. For example, adding a small P-dopant to an inverter will alter its functionality to a fixed output.
IC protection?
Although they are legally protected by copyright, some techniques are coming out for Hardware Protection:
IC metering: Lock the circuits with an unique on-chip key. This fingerprint is generated by an on-chip physical unclonable function (PUF) or a true random number generator (TRNG)
Watermarking: add a kind watermark hidden in the netlist. So you could detect later, who is the malicious partner.
For example, the transistor width is modified by adding a bit, but still the width is inside the technology tolerance, so it will not affect to the transistor real width at fabrication. But you can detect it scanning the netlist.
IC camouflaging: This technique consists of adding dummy structures to the layout to generate confusion and cheat the reverse engineering process.
This is very curious:
For example, by adding a small P-dopant to an inverter, you can modify the inverter in a predictive manner, leaving a floating output or setting it to VDD.
Another example: The width of a transistor determines its strength. In almost 100% of the cases, the full gate area is doped, right? but if you partially doped the gate of a CMOS, let’s say 10% of the active area, there is no way to know the exact measures of that transistor. [3]
Split manufacturing: The circuit layers are split in two, front end of line (FEOL) and the back end of line (BEOL) containing the lower and upper layers respectively. The two groups of layers are manufactured in different foundries. This prevents from overproduction in an untrusted foundry, but still the second fab could easily reverse engineer the circuit discovering the connections between both groups. Another drawback is that defective and out-of-spec parts from the button layers can not be recognized directly.
Logic locking: the most effective. This technique is very well known in the software industry
Although the IP (Intellectual Property) anti-copy regulation, in the last years some untrusted entities will be always there.
References
[1]: “Towards Provably-Secure Analog and Mixed-Signal Locking Against Overproduction”
[2]: “The use of digital image processing for IC reverse engineering”
[3]: “Stealthy dopant-level hardware Trojans: extended version”
[4]: “Winning the battle against counterfeit semiconductor products” (SIA) Anti-Counterfeiting White Paper. 2013